15 Tips for Online Safe Shopping
Written by Kim Porter for NortonLifeLock
Online shopping is easy to love. What’s more fun than finding what you need and—after a few clicks and a short wait—having it show up at your door
Except when it doesn’t. In 2016, the FBI’s Internet Crime Complaint Center received nearly 300,000 online-theft complaints, and victims lost a total of $1.3 billion. It’s safe to say fake companies and identity thieves can turn the joy of buying into a hassle.
What to do? Don’t click that buy button until you check out these tips to help you do safe online shopping.
- Shop where you trust
Shopping IRL (in real life) offers this advantage: You’ll usually know the business and the inventory exist. But on the web, some businesses are fabricated by people who just want your credit card information and other personal details. Consider doing online business only with retailers you trust and have shopped with before.
- Size up the business
Break out your detective skills when you want to buy something from a new merchant. Does the company interact with a social media following? What do its customer reviews say? Does it have a history of scam reports or complaints at the Better Business Bureau? Take it one step further by contacting the business. If there’s no email address, phone number or address for a brick-and-mortar location, that could be a red flag that it’s a fake company.
- Beware rock-bottom prices
If a website offers something that looks too good to be true—like rock-bottom prices or an endless supply of free smartphones—then it probably is. Use similar websites to compare prices and pictures of the merchandise. Perpetually low prices could be a red flag that the business doesn’t have those items in stock. The website may exist only to get your personal information.
- Avoid public Wi-Fi
Wi-Fi networks use public airwaves. With a little tech know-how and the freely available Wi-Fi password at your favorite coffee shop, someone can intercept what you’re looking at on the web. That can include emails, browsing history or passwords. Shopping online usually means giving out information that an identity thief would love to grab, including your name and credit card information. Bottom line: It’s never a good idea to shop online or log in to any website while you’re connected to public Wi-Fi.
- Use a VPN
If you must shop online on public Wi-Fi, use a VPN (virtual private network). A VPN creates an encrypted connection between your computer and the VPN server. Think of it as a tunnel your Internet traffic goes through while you browse the web. Hackers lurking nearby can’t intercept it, even if they have the password for the Wi-Fi network you’re using. A VPN means you’ll likely have a safe way to shop online while you’re on public Wi-Fi.
- Use a strong password
If someone has the password to your account, they can log in, change the shipping address, and order things while you get stuck with the bill. Help keep your account safe by locking it with a strong password. Here are some tips on how:
- Use a complex set of lowercase and uppercase numbers, letters, and symbols.
- Avoid words that come from a dictionary.
- Don’t use personal information that others can find or guess, such as birthdates, your kids’ names or your favorite color.
- And don’t use the same password—however strong—on multiple accounts. A data breach at one company could give criminals access to your other, shared-password accounts.
- Check out the webpage security
You’ve probably seen that small lock icon in the corner of your URL field. That lock signals you that the web page you’re on has privacy protection installed. It’s called a “secure sockets layer.” Plus, the URL will start with “https,” for “hyper text transfer protocol secure.” These websites mask and transfer data you share, typically on pages that ask for passwords or financial info. If you don’t see that lock or the “s” after “http,” then the webpage isn’t secure. Because there is no privacy protection attached to these pages, we suggest you exercise caution before providing your credit card information over these sites.
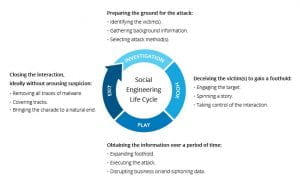
- Watch out for email scams
Sometimes something in your email in-box can stir your consumer cravings. For instance, it might be tempting to open an email that promises a “special offer.” But that offer could be special in a bad way. Clicking on emails from unknown senders and unrecognizable sellers could infect your computer with viruses and malware. It’s better to play it safe. Delete them, don’t click on any links, and don’t open any attachments from individuals or businesses you are unfamiliar with.
- Don’t give out more information than you need to
Here’s a rule of thumb: No shopping website will ever need your Social Security number. If you’re asked for very personal details, call the customer service line and ask whether you can supply some other identifying information. Or just walk away.
- Pay with a credit card
When using a credit card, you’ll usually get the best liability protection—online and offline. Here’s why.
If someone racks up unauthorized charges on your credit card, federal regulations say you won’t have to pay while the card company investigates. Most major credit cards offer $0 liability for fraudulent purchases.
Meanwhile, your liability for unauthorized charges on your debit card is capped at $50, if you report it within two business days. But if someone uses your account and you don't report the theft, after 60 days you may not be reimbursed at all.
- Try a virtual credit card
Some banks offer nifty tools that act like an online version of your card: a virtual credit card. The issuer will randomly generate a number that’s linked to your account, and you can use it anywhere online and choose when the number expires. It might be best to generate a new number every time you buy something online, or when you shop with a new retailer. Anyone who tries to use that number will be out of luck.
- Check your statements regularly
Check your statements for fraudulent charges at least once a week, or set up account alerts. When you receive a text or email about a charge, you can check the message and likely easily recall whether you made the charge.
- Mind the details
After you make the purchase, keep these items in a safe place: the receipt, order confirmation number and postal tracking number. If you have a problem with the order, this information will help the merchant resolve the problem.
- Take action if you don’t get your stuff
Call the merchant and provide the details noted in Tip 13. If the merchant turns out to be fake, or they’re just plain unhelpful, then your credit card provider can help you sort out the problem. Often, they can remove the charge from your statement.
- Report the company
If you suspect the business is bogus, notify your credit card company about the charge and close your account. File a complaint with the U.S. Federal Trade Commission. Tip: The FTC offers an identity theft recovery plan, should you need it.