Human Error and Information Security Hygiene
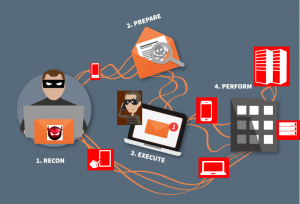
95% of all successful cyberattacks start with human error according to the IBM Cybersecurity Intelligence Index. That would make it pretty important to periodically evaluate and increase your own awareness of Information Security hygiene and awareness.
Information security is one of the fastest-changing fields in the world. New technologies emerge every day that change the way people attack and defend systems and networks. While professionals in information security are required to be in a constant state of learning to keep up with the field as a whole, those without day to day dealings tend to be the primary targets and the least informed. Being aware and informed enables everyone to protect themselves.
Awareness Companies
Security awareness training should be a high priority for any organization. To facilitate effective awareness training, a number of companies focus on providing awareness training as a professional service, often using computer based training. Companies such as Habitu8, SANS, KnowBe4, and Security Ninja focus on providing awareness training packages to organizations who want to inform and educate their employees.
These packages are frequently integrated into something called a learning management system (LMS). An LMS is something like Blackboard.
Other free resources are also essential to reach people both inside and outside the Information Security community, such as:
- SANS Resources: SANS Security Resources
- Khan Academy Quiz: Cybersecurity 101 Quiz
- GW Resources: you can email infosec@gwu.edu for more resources or to request training for your student organization or department.
On the Web
While organized and mandatory awareness training can be effective, it isn’t the only way to reduce risk and stay up to date on cybersecurity. There are an abundance of websites, blogs, and other informational pages freely available to all. Cybersecurity is often in the news, and the following websites can help users stay up to date:
- Have I Been Pwned (run by Troy Hunt) lets users check if their email has been associated with a data breach and stay informed on breaches happening worldwide.
- Krebs on Security: Brian Krebs’ site offers in-depth coverage of ongoing security stories without overwhelming less technical readers.
- Credit Karma and Equifax offer credit monitoring services that can track your exposure to identity fraud or credit data breaches.
Social Media in Security
As social media has gained popularity, more and more professionals are turning towards it to keep informed and spread their message. It may come as a surprise to some that there is a large information security community on twitter. The #infosec community on Twitter is one of the best places to keep up with the latest security news. Professionals and organizations share news, tips, and resources.
Key accounts to follow:
- Jake Williams (@MalwareJake)
- Brian Krebs (@briankrebs)
- Troy Hunt (@troyhunt)
- Lesley Carhart (@hacks4pancakes)
- Organizational Accounts:
- National Cyber Alliance (@StaySafeOnline)
- SANS Internet Storm Center (@sans_isc)
These accounts provide invaluable resources for staying aware of current security trends, free webinars, blogs, and more.