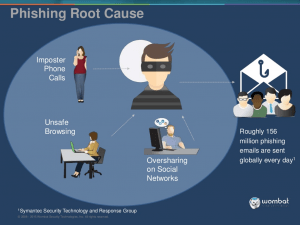
Reports have surfaced of a vulnerability within the chat function of Zoom for Windows that may permit unauthorized access to online classes and video conferences, which may allow hackers to send a malicious link through Zoom chat.
The malicious link looks slightly different from a URL, but is similar enough to cause confusion for users. When the link is clicked, the user’s credentials (UserID and password) may be leaked online. Leaked passwords can be easily cracked with widely available tools. In addition, hackers could gain access to the user's computer, execute unwanted software, send malicious messages, etc.
While there have been no known impacts to GW accounts, please follow these recommendations for video meetings and online instruction:
- Use Webex instead of Zoom. Webex is GW’s supported secure video meeting collaboration tool, and is available to all students, faculty and staff. Visit the telecommuting page to learn more.
- For online instruction, use Blackboard, GW’s online learning platform. Blackboard allows faculty to share materials with students, as well as facilitate synchronous (Blackboard Collaborate) and asynchronous communications (including discussion boards and integrations with VoiceThread and Echo360). Visit the tools for instructional continuity page to learn more.
- Use meeting passwords for all meetings, verify all participants, and lock entry. To learn how to host secure Webex meetings and lock entry, visit Webex Secure Meetings.
- Do not share or click on any links from unknown users.
- Avoid links that start with a double back slash (e.g. \\ for example, \\com).
Remember to protect your information!
GW Information Technology (GW IT) continues to take proactive measures to keep our campus community safe. Please be aware that phishing attempts often seem legitimate. It is important for faculty, staff, and students to be extremely vigilant and take steps to secure logins, passwords, and data.
GW’s Office of Ethics, Compliance and Privacy has developed guidance on best practices for data protection when telecommuting, as well as data protection while using virtual meeting, event and collaboration platforms. Visit COVID-19 data protection guidance to learn more.
Remember to report any suspicious electronic communication or request to abuse@gwu.edu.
Questions? Concerns? Please contact GW Information Technology at 202-994-GWIT (4948), ithelp@gwu.edu or IT.GWU.EDU.